In a past blog post, I talked about the value of the D3FEND™ Matrix for identifying mitigating controls. In this blog post, I wanted to focus on the “deceive” tactic. This tactic is used “to advertise, entice, and allow potential attackers access to an observed or controlled environment.”
What is Cyber Deception?
Cyber deception is not a new concept, but has been getting more attention in recent years as various industry reports highlight the “dwell time,” or the amount of time that passes between an attacker’s actions and the victims identifying or detecting the activity. One example of these reports is the 2021 Ponemon Institute Cost of a Data Breach study, which notes that on average it takes over nine months to detect and contain a data breach.
Cyber detection controls such as honey pots, decoy files, and decoy credentials are aimed to increase the detection rates of attackers and ideally shorten the detection timeline. You can think about each deceptive control as an additional tripwire with alarm bells attached, that the attackers need to bypass without raising the alarm.
Who Should Consider Implementing Cyber Deception Controls?
Cyber deception controls are not entry-level controls. Organizations should focus on building a strong foundational security program before considering any of these recommendations. If you are starting to build a new program, you should first implement some of the earlier tactics from D3FEND, such as documenting your environment (hardware and software inventories, network mapping, etc.) and hardening the assets you’re tracking. Once you have those things in place, you’ll want to have a strong detection environment and can collect and analyze event logs to generate meaningful alerts. All this needs to come before building out deception to make sure your efforts are being spent in the areas you will see the largest return. These foundational controls will reduce the likelihood of attackers getting into your systems, while the deceptive controls will only generate alerts that they are already inside.
What Does it Look Like?
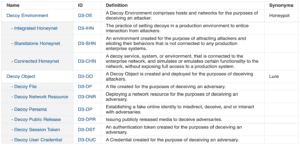
At the time of writing this blog post, D3FEND lists 11 deceptive controls:
As an illustrative example, we’re going to look at how the “Decoy User Credential” control can be used to reinforce the concepts discussed in our recent post about a Tiered Administrative Strategy in Active Directory. To create a decoy user account that would indicate there are malicious actors in our network, we’d want to make the account look like an administrative account that, not knowing about the tiered approach, could be used for general administration of machines. Something with a name like “IT-Admin” will be enticing by name, but we’ll need to make sure the other user attributes are made to look normal and not stand out as an obvious decoy. If it looks obvious, the attacker won’t use it and our trip wire will remain silent.
Some of the notable attributes you will want to configure are:
- Group membership
- Logon hours
- Last logon
- Password never expires
- Smart card is required for interactive login
- Store password using reversible encryption
- Utilize the “Description” field with password “hints”
- User cannot change password
The aim with configuring these attributes is to make the account look like a legitimate administrative account that someone got sloppy and left a note in the description field, but also making sure that the account cannot be used by an attacker to log in.
The final step is to configure an alert for any attempted authentication activity with this target account. Anyone trying to use this account should be considered highly suspicious and your incident response process should be invoked to fully investigate.
Where to Learn More
While this is a brief introduction to deception controls, there is a lot of exciting work being done in this space. If you’re looking to learn more about cyber deception controls, the following resources will get you started: